Weaksystemssecuritypracticesarebeingexploited
You’re only as strong as your weakest link. Here’s a rundown of some good systems security practices to help you to avoid commonly exploited controls and practices that are routinely allowing bad actors to take initial access.
The joint Cybersecurity & Infrastructure Security Agency recently issued an advisory alert1 for commonly exploited controls and practices that allow bad actors to take initial access to victims’ networks.
So here’s our rundown of the identified mitigations in that alert. Plus some thoughts on how you go about implementing these mitigations. We hope you can use this as a good starting point to ask about your organisation’s security.
Here's the rundown:
enforce Multifactor Authentication
Multifactor Authentication, or MFA, is the practice of requiring a user to prove it’s them logging in multiple ways. That could be a password and a one-time password to log in too. This practice is especially important for businesses that have people accessing business applications remotely, for example by using the Remote Desktop Protocol.
Implementing MFA can help stop account takeovers. The alert especially highlights the importance of ensuring that all users do this. Having users with administrator-level access and being excluded from the MFA could be a recipe for disaster.
check access permissions and access control lists
Incorrectly applied permissions can give users more access than they need. That has the potential for users to change things that should not be changed or to grant access to unauthorised users or system processes.
Mistakes happen, and people and their required permissions change over time. Regular checking and the application of least privileged access, or, a zero-trust security model can help prevent security incidents from both external threat actors and internal acts such as malfeasance, negligence, or just accidents.
keep all software up to date
This is one area where clicking the ‘remind me later’ button can be harmful. Software updates aren’t just full of feature and compatibility updates, they often also include security updates. Unpatched software may allow unauthorised access. When software updates are issued, they could be fixing known vulnerabilities.
However, it can be an easy thing to miss and control. For example, it can rely on all users dutifully updating their devices. Updates can fail or cause compatibility issues. Your IT estate might be large and heterogeneous. There might be hidden tools and devices being used.
Software lifecycle management, endpoint management and network monitoring tools can all help with managing some of these challenges.
check defaults - both settings and passwords
Check the defaults across your software, hardware and networks. Preconfigured and default settings are a double-edged sword. They are there to help be more user friendly… but potentially at the cost of security. For instance, your network may use well-known passwords, easy to guess passwords, or, the credentials to your router may even be printed on the box!
The same with ports. Open ports aren't necessarily dangerous. But the system and network configuration around it can determine whether they are exploitable. In some cases, it may be best to close them.
enable and enforce good password policies
All lowercase and text-based passwords are easy to crack. An 8 letter password may have 209 billion possible combinations, but a computer can crack that instantly.2
Good password policies may include things like:
- Being unique across all log-ins
- Including a mix of upper and lower case, numbers, and special characters
- Not being shared
- If stored, being stored securely
It’s a good idea to set up your system so that it won’t accept common passwords. But also help to enable your employees to have good password practices by making it easier for them. By providing a password manager for instance.
Many business-focused password managers also feature the addition of one-time passwords for each account or password entry.
check your cloud services’ security configurations
Misconfigured and outright unprotected cloud services can be a massive security risk. The Cybersecurity & Infrastructure Security Agency advisory specifically mentions that poor configurations can allow unauthorised access. This weakness could lead to data loss or even the use of the servers for crypto-jacking.
For cloud environments, it’s important to set up roles and network security groups that keep different roles such as developers and operators from needing to build their own security profiles. Not doing so from the get-go can open up the potential for human error and poor security configuration later on.3
Ultimately, the use of public cloud services comes with a shared responsibility model. What the provider and what your responsibilities are may change both with the provider you select and the type of services you are consuming.
Here’s a broad and vendor-agnostic overview of where the responsibilities sit between cloud users and cloud providers:
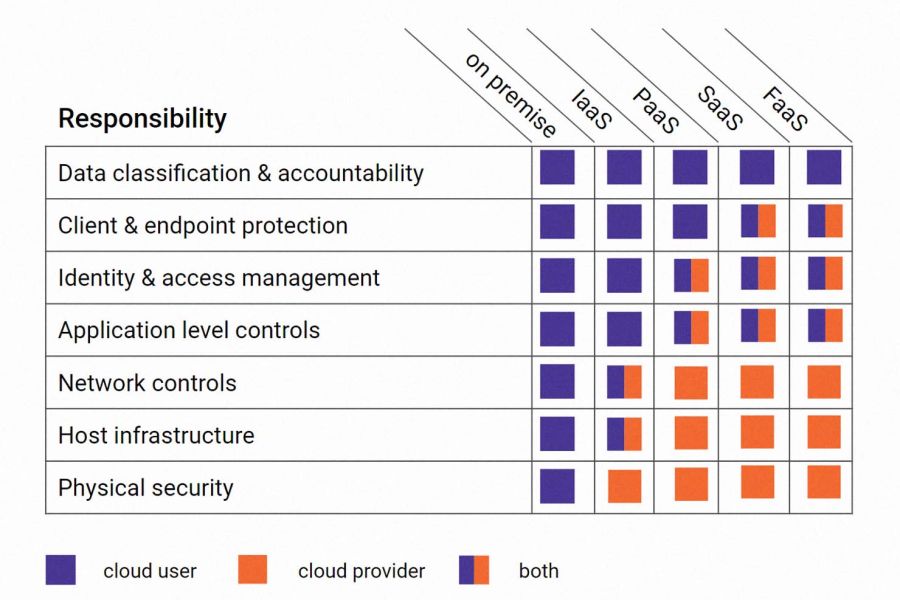
Above we’ve shown a vendor-agnostic overview of where the responsibilities sit between cloud users and cloud providers.4
Understanding your responsibilities and your cloud provider(s) is just the beginning. The creation of policies and procedures to make it happen is just as important, as well as, the use of cloud security tools to monitor the environments too.
Psst… Check out our recent protecting cloud workloads webinar featuring a guest speaker from cybersecurity technology company CrowdStrike.
detect and respond
Detection comes in many forms. For example:
- Monitoring for compromised log-ins and passwords across your environment or things like published API keys
- Implementing a centralised log management system and setting up alerts
- Running anti-virus tools on user devices and monitoring/acting on the scan results
- Running detection tools across networks and cloud environments
- Actively looking for vulnerabilities. Such as, running the cloud providers’ vulnerability scanning tools and conducting penetration testing
prevention is the best cure
Did you know that 95% of cyber security issues can be traced to human error?5 Creating the right environment, from onboarding into regular cyber security training, having the right tools and security audits, and even drawing on third-party support can go a long way in helping you avoid unwanted cyber security incidents.
To draw on a proverb, the best time to act was yesterday, the next best time is today.
references
1 Cybersecurity & Infrastructure Security Agency, ‘Alert (AA22-137A)
Weak Security Controls and Practices Routinely Exploited for Initial Access’, 17th May 2022.
2 World Economic Forum, ‘This chart shows how long it would take a computer to hack your exact password’, 7th Dec 2021.
3 CrowdStrike, ‘2022 Global Threat Report’, accessed 19th May 2022.
4 Full details of the ‘big 3’s’ shared responsibility models are available on their websites: AWS, Microsoft and Google Cloud.
5 World Economic Forum, ‘The Global Risks Report 2022’, 11th January 2022